The need was straightforward: share large files — tens of gigabytes of raw footage, project archives, training videos — without going through a third-party cloud. No Google Drive, no WeTransfer, no Dropbox. A dedicated server, files you control, links that expire when you want them to. The result: ShareBox, a self-hosted file sharing platform with integrated video streaming, written in pure PHP 8.1 with no framework.
The repo is on GitHub.
Zero runtime dependencies
The first decision — and the most consequential — was to avoid any framework.
No Symfony, no Laravel. Pure PHP, native stdlib, SQLite auto-created on first boot.
Composer is present, but only as a dev dependency for PHPUnit. In production,
no vendor/ directory is needed.
This constraint is clarifying. Every feature must justify its real implementation cost — not outsourced to a package that does ten times what you need. Manual routing in a few dozen lines, native PHP session handling, SQLite queries via PDO: these are things you implement once and understand completely.
SQLite followed the same logic — no server to configure, no complex migrations,
the database file lives next to the code and backs up with a simple cp.
For a single-instance tool, it's more than enough.
The installer follows the same principle — a one-liner for Debian/Ubuntu:
curl -sSL https://raw.githubusercontent.com/ohugonnot/sharebox/main/install.sh | bashA script that installs system dependencies, configures Apache or nginx, creates the SQLite database, and sets correct permissions. No Docker required, no registry to contact.
The real challenge: video streaming
Sharing a text file or a ZIP archive is trivial. Sharing a video and letting someone watch it directly in the browser — with seek, audio track selection, subtitles — is a different problem.
The first decision was to avoid systematic transcoding. If the file is already in a browser-compatible format (H.264/AAC in an MP4 or MKV container), we do a remux on the fly: repackage the existing streams without re-encoding. FFmpeg takes a few seconds, CPU usage is near zero, and quality is identical to the source.
Full transcoding only kicks in when necessary — typically for HEVC/x265 files, which very few browsers decode natively. In that case, FFmpeg transcodes to H.264 on the fly, with quality selection: 480p, 720p, or 1080p.
Seek in a live-transcoded stream is the trickiest part. A Range: bytes=...
request on a classic HLS stream works because segments are pre-generated. Here, the
stream is generated in real time — so seek means restarting FFmpeg with -ss
at the right timecode, rather than seeking a byte offset in an already-generated file.
The code orchestrating this in stream.php is worth reading if you're
tackling a similar problem.
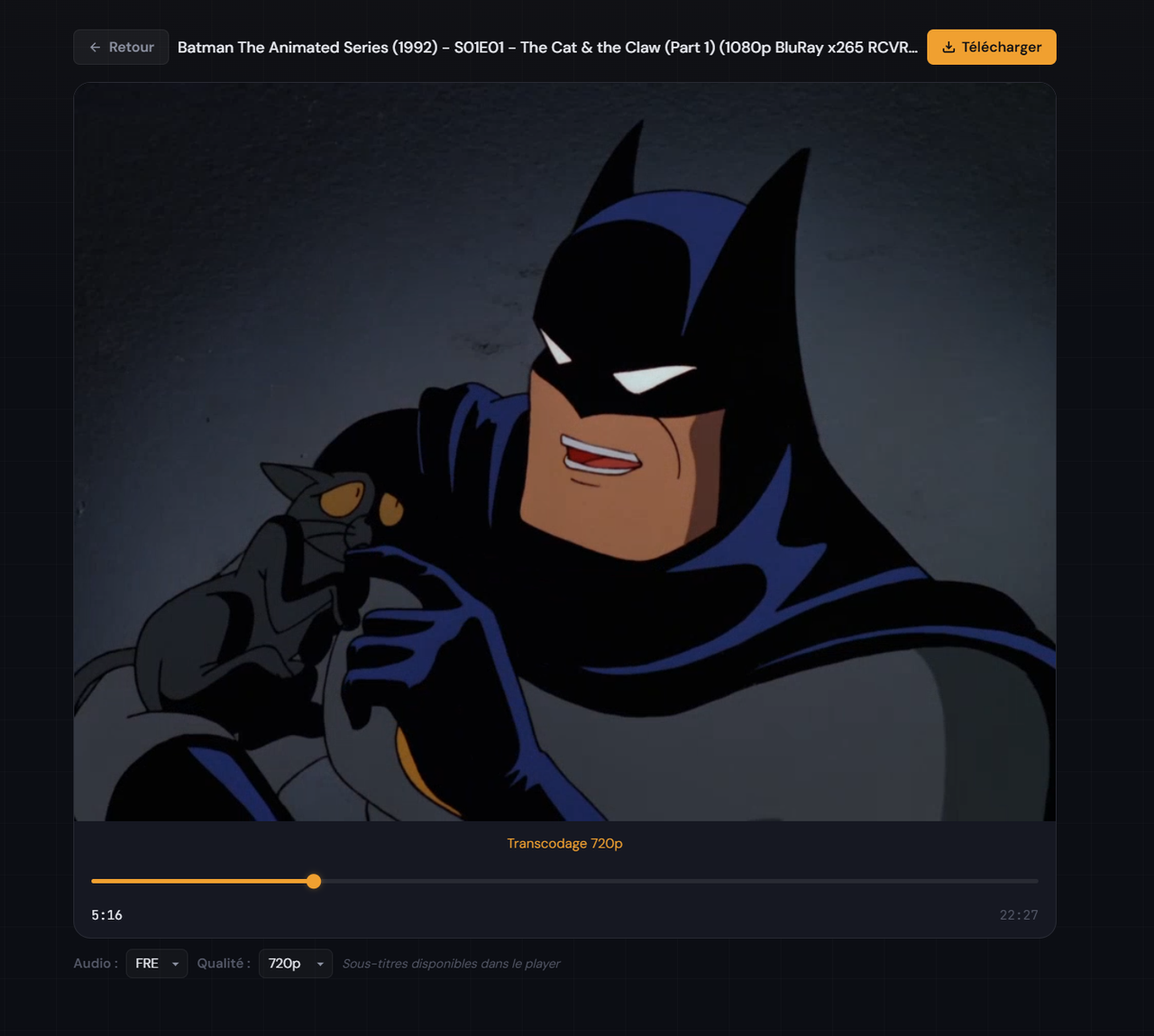
The integrated video player: native seek, quality selection, WebVTT subtitles.
Human-readable slugs
A UUID to identify a share is secure but unusable by humans. Getting
/dl/3f7a2c1d-8b4e-4f9a-b2d6-1c5e8f3a7b2c in an email is opaque.
ShareBox generates slugs from the filename:
batman-begins-2005.mkv → /dl/batman-begins-2005-x7k2
The 4-character random suffix is enough to avoid collisions without sacrificing
readability. batman-begins-2005-x7k2 tells you immediately what it
contains, is easy to copy by hand, and survives a message or URL without issues.
Slug generation normalizes the string: accent transliteration, lowercase conversion, replacement of spaces and special characters with hyphens, removal of consecutive hyphens. The result is then checked against the database for uniqueness before insertion.
Security without a framework
A framework quietly handles a lot of security concerns — often without the developer being aware of it. Without a framework, these concerns must be addressed explicitly. Four stood out as needing careful attention.
Directory traversal. When serving files from disk, you have to ensure
a parameter like ../../../etc/passwd doesn't get through. The solution:
realpath() on the resolved path, then verify the result is a subpath of
the allowed upload directory. If the resolved path escapes the target directory,
the request is rejected.
CSRF protection. The admin panel exposes destructive actions (file deletion, link revocation). Every POST form includes a CSRF token stored in session, regenerated after each sensitive action.
Session fixation. After authentication, session_regenerate_id(true)
is called to invalidate the old session identifier and issue a new one. Without this,
an attacker who knows the session ID of an unauthenticated visitor can reuse it after login.
Mail header injection. The email sharing form accepts a destination address. Without strict validation, an attacker can inject additional SMTP headers into the email field and hijack the outgoing message. All user inputs destined for mail headers are filtered to strip newlines before being passed to sending functions.
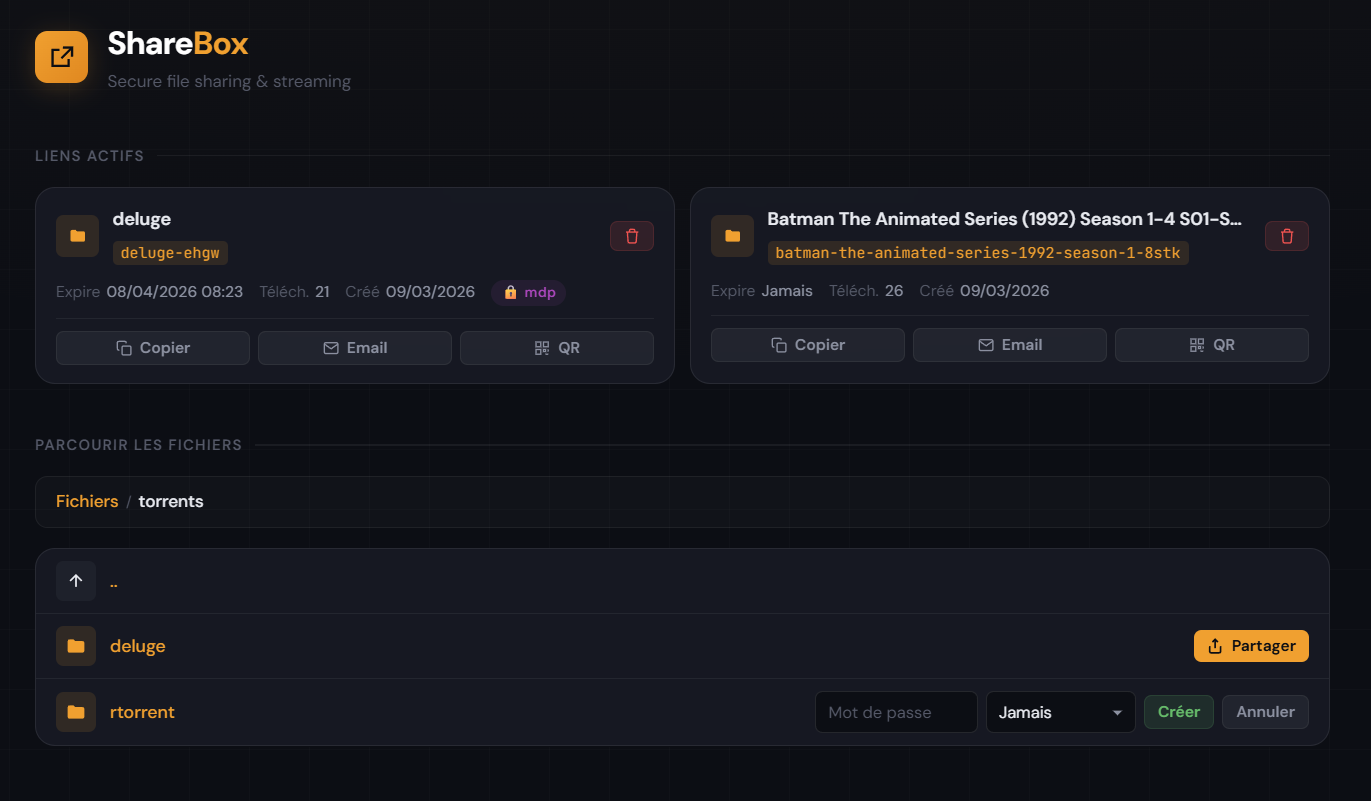
The admin panel: share management, expiration, password protection.
Tests: what's actually worth covering
44 PHPUnit tests, no mock framework, no external test dependency. The question wasn't "how to test everything" — it was "what breaks silently if we don't test it."
Three categories stood out as particularly valuable:
Slugs. Slug generation is a pure function with many edge cases: names with accents, multiple spaces, Unicode characters, collisions, filenames without extensions. Thorough tests on this function are worth their weight in gold — it's exactly the kind of code that looks trivial and breaks unexpectedly on real input.
Format detection. The logic deciding whether a video can be remuxed or must be transcoded relies on reading FFprobe metadata. Testing with FFprobe output fixtures for different codecs (H.264, HEVC, VP9, AV1) ensures the remux/transcode decision is correct without needing actual video files in the test suite.
Security. Directory traversal tests, header injection tests, and CSRF token validation tests are the most valuable. These are well-documented attack vectors, easy to test with known payloads, and missing an edge case has direct consequences.
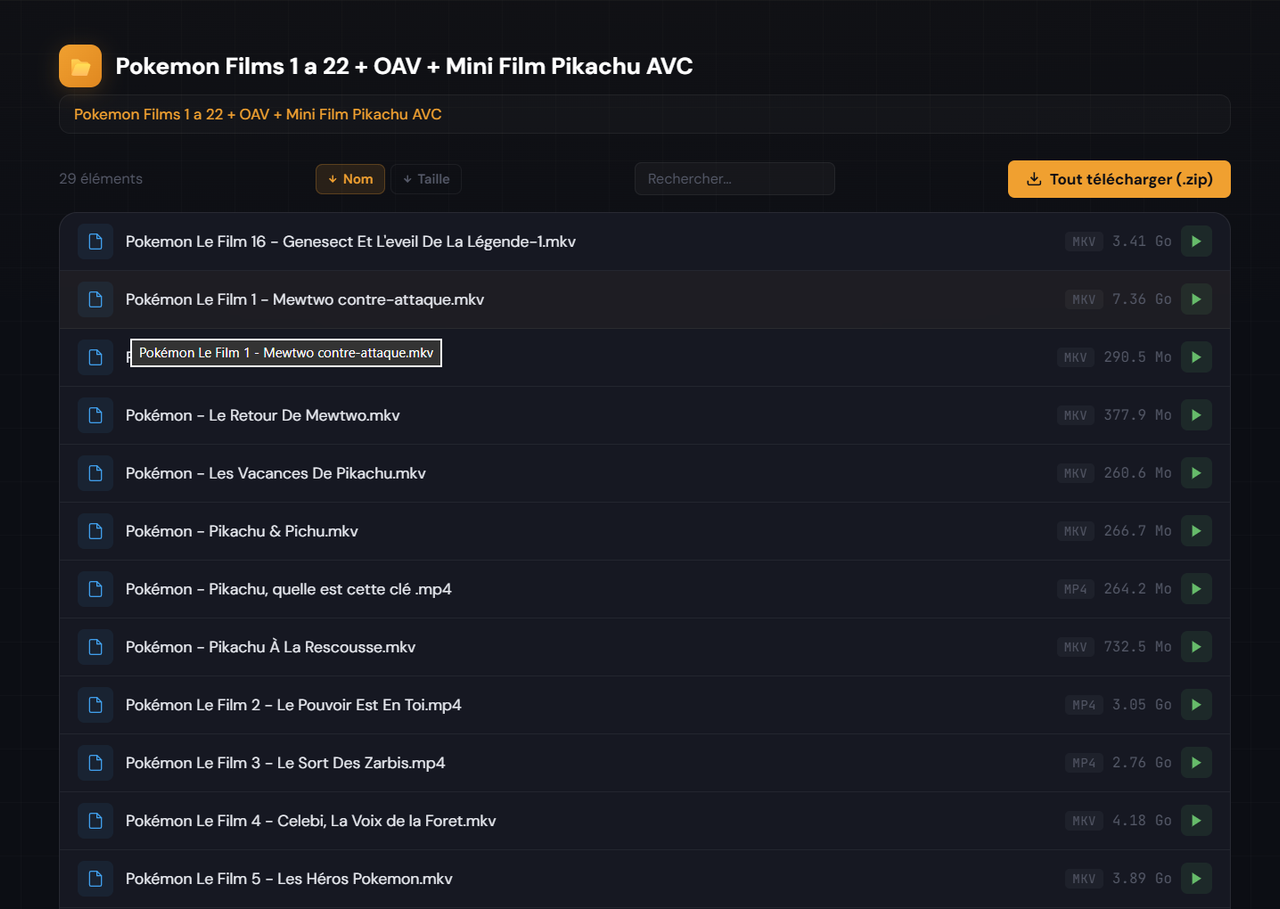
Folder sharing: file browsing, one-click ZIP download.
Key takeaway
The "zero runtime dependencies" philosophy isn't a stance. It's a commitment to understanding and maintaining what you build. Every line of code in ShareBox has an explicit reason to exist — no magic hidden in a third-party component whose source you've never read.
The concrete lesson from this project: PHP is capable of adaptive video streaming, seek in live transcoding, and correct security — with no framework whatsoever. The difficulty isn't in the language; it's in understanding what you're building.
The code is available at github.com/ohugonnot/sharebox.